The Education Cybersecurity Maturity Stack
Every school, district, and university sits somewhere on a four-layer maturity stack that determines whether a breach is a matter of "if" or "when is the recovery." The stack works bottom-up: skip a layer and the ones above it crumble.
| Layer | Focus | Key Components |
|---|---|---|
| 1. Compliance Foundation | Legal baseline | FERPA, COPPA, CIPA, state privacy laws, GLBA (higher ed financial aid) |
| 2. Governance Framework | Strategic risk management | NIST CSF 2.0, CIS Controls, risk assessments, policy documentation |
| 3. Operational Defense | Technical controls | MFA, network segmentation, endpoint detection, backup testing, vendor management |
| 4. Security Culture | Human resilience | Phishing simulations, role-based training, incident response rehearsals |
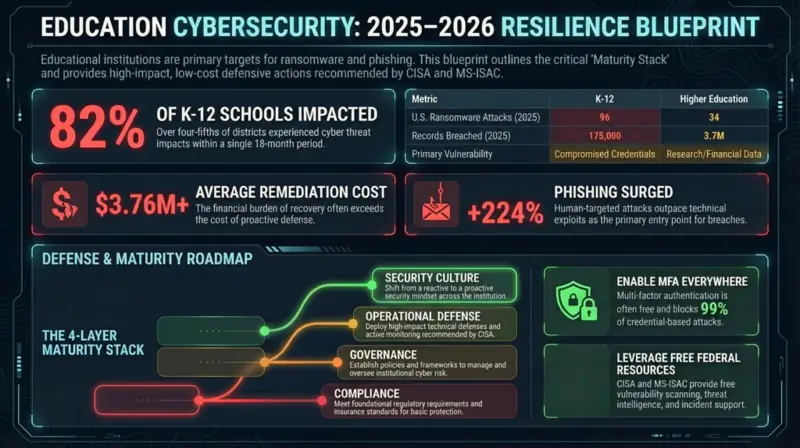
The 2025 CIS MS-ISAC report found that 82% of K-12 schools experienced cyber threat impacts over an 18-month period, with human-targeted attacks outpacing technical exploits by 45%. That gap between layers 3 and 4 is where most education breaches live. For a broader view of how NIST CSF 2.0 maps to your security stack, start there.
The Compliance Foundation: What the Law Actually Requires
Educational institutions juggle a patchwork of federal and state regulations, none of which were written with ransomware in mind. FERPA, the heavyweight, protects student education records but contains no explicit cybersecurity requirements. The Department of Education infers security obligations from FERPA's "reasonable methods" language, leaving districts to interpret what "reasonable" means when a threat actor has AI-generated phishing kits. Non-compliance can cost an institution its federal funding, which for most schools is existential.
COPPA applies when schools approve third-party apps that collect data from students under 13. CIPA mandates internet filtering for any school using E-Rate discounts. For higher education institutions handling financial aid data, GLBA's Safeguards Rule now requires written information security plans with designated coordinators, risk assessments, and vendor oversight. State laws add another dimension: as of 2025, over 40 states have enacted student privacy statutes that exceed federal minimums.
Federal Compliance Requirements for Education
| Regulation | Applies To | Core Requirement | Non-Compliance Penalty |
|---|---|---|---|
| FERPA | All institutions receiving DoE funding | Protect education records; "reasonable methods" for access control and authentication | Loss of federal funding |
| COPPA | Schools using platforms collecting data from children under 13 | Parental consent before collection; privacy policy; data minimization | FTC fines up to $50,120 per violation |
| CIPA | Schools and libraries using E-Rate discounts | Internet filtering; safety policy; student education on online behavior | Loss of E-Rate funding |
| GLBA Safeguards Rule | Higher ed institutions handling financial aid | Written security plan; designated coordinator; vendor oversight | FTC enforcement actions |
| NIST SP 800-171 | Institutions with DoD contracts or grants | 110 security controls for Controlled Unclassified Information | Loss of contract eligibility |
"Schools should be mandated to have a level of cyber posture, but they should only reasonably expect that to happen if it's funded."
Elliott Lewis CISO, ParentPay Group, as quoted in Infosecurity Magazine
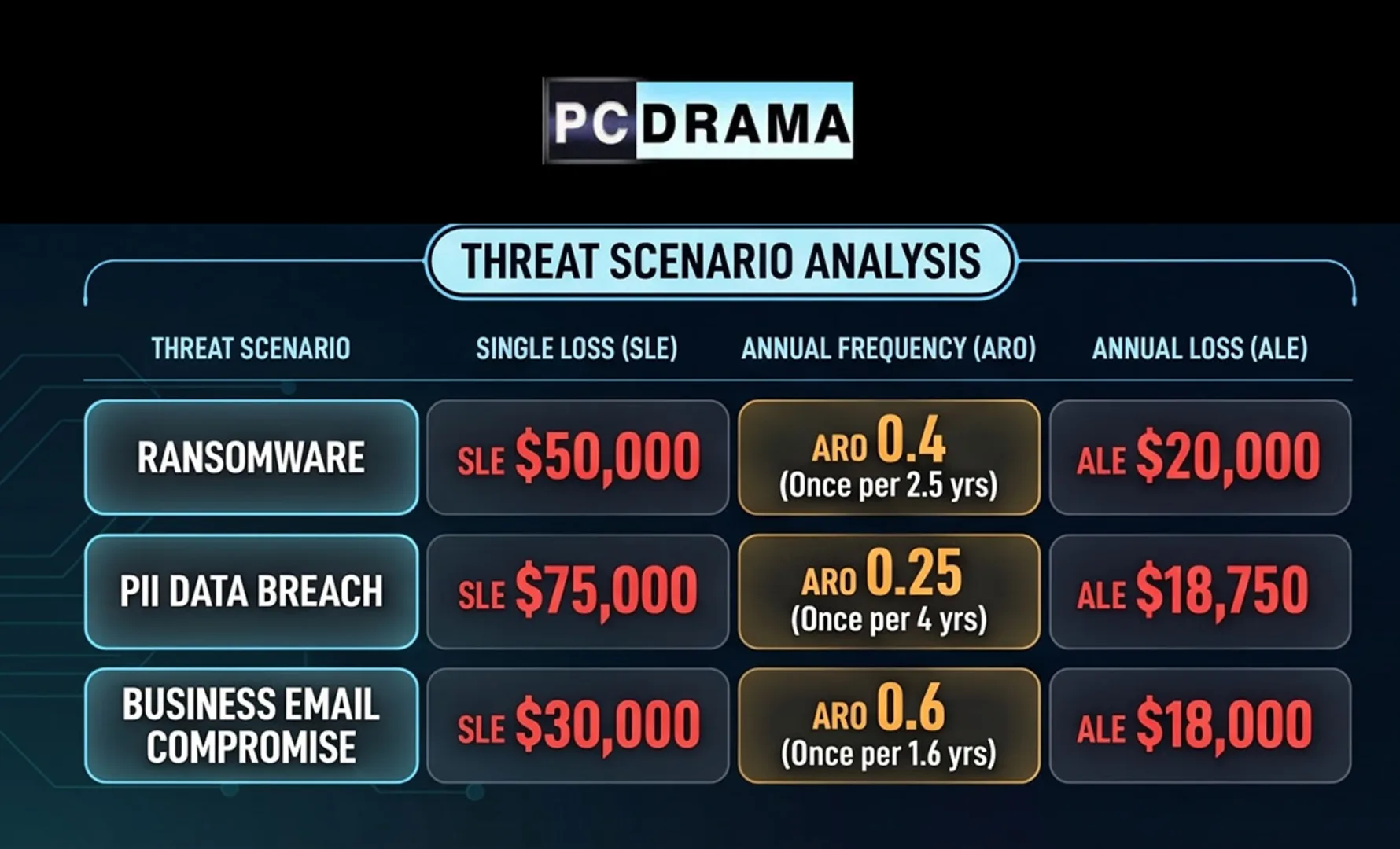
Threat Landscape by the Numbers
Education is the third most targeted sector globally. In the first half of 2025, ransomware incidents jumped 23% year over year, with 130 known incidents in the U.S. alone. By year's end, 251 ransomware attacks hit educational institutions worldwide. The average ransom demand settled at $464,000 (down 33% from 2024), but recovery tells the real story. For a deeper dive into these threats, see our education sector threat analysis.
| Metric | K-12 | Higher Education |
|---|---|---|
| U.S. ransomware attacks (2025) | 96 | 34 |
| Average remediation cost | $3.76M | $4.02M |
| Records breached (U.S., 2025) | 175,000 | 3.7M |
| Average ransom demand (2025) | $464,000 | |
| Phishing surge (2024 YoY) | +224% |
The asymmetry is striking: K-12 gets hit nearly three times as often, but higher education breaches expose 20 times more records per incident. Universities hold research data, financial aid records, and decades of alumni information. K-12 districts face more frequent but lower-sophistication attacks, often because a single compromised teacher credential opens the door to the student information system.
Attack Vectors: How K-12 and Higher Ed Get Breached Differently
| Attack Vector | K-12 Prevalence | Higher Ed Prevalence | Why It Works |
|---|---|---|---|
| Phishing and social engineering | Very high | High | Large, rotating user populations with minimal security training |
| Credential stuffing | High | Very high | Students reuse passwords across personal and institutional accounts |
| Ransomware (direct deployment) | Very high | High | Pressure to restore services quickly; often no tested backups |
| Third-party vendor compromise | High | Medium | K-12 relies heavily on SIS vendors; single points of failure |
| Nation-state targeting | Low | High | Research in AI, biotech, and quantum computing attracts state actors |
| Insider threats | Medium | Medium | Open academic culture prioritizes access over restriction |
Building the Defense Stack (Without the Budget)
The education sector's chronic funding gap is no secret. While healthcare and finance allocate 10-15% of IT budgets to cybersecurity spending, most school districts operate with a fraction of that. The good news: the highest-impact defenses are not the most expensive ones. CISA and MS-ISAC provide free threat intelligence, incident response support, and vulnerability scanning specifically for education. K12 SIX, the sector's information sharing community, offers peer intelligence at no cost.
The institutions weathering attacks best share a pattern: they enforce multi-factor authentication on all remote access, maintain tested offline backups that ransomware cannot encrypt, segment student networks from administrative systems, and run regular phishing simulations. None of these require enterprise budgets. They require configuration changes, time, and someone who knows what "reasonable" actually looks like in 2026.
CISA's Essential Cybersecurity Actions for K-12
| Action | Cost | Impact |
|---|---|---|
| Enable MFA on all remote access and admin accounts | Free (built into most platforms) | Blocks 99%+ of credential-based attacks |
| Join MS-ISAC for threat intelligence and incident support | Free | Real-time alerts; incident response assistance |
| Implement network segmentation (student vs. admin) | Low (VLAN config) | Contains lateral movement from compromised devices |
| Maintain and test offline backups | Low to moderate | Eliminates ransomware payment leverage |
| Run quarterly phishing simulations for staff | Free to low | Reduces successful phishing by 60-80% over time |
| Develop and rehearse an incident response plan | Time investment | Reduces recovery time and cost by 30-50% |
| Vet third-party vendors for security practices | Time investment | Prevents supply-chain breaches (see: PowerSchool) |
Frequently Asked Questions
About Education Cybersecurity
- CISA: Cybersecurity for K-12 Education — Federal guidance, toolkits, and free resources for schools
- K12 SIX — The K-12 sector's information sharing and analysis organization
- CIS 2025 K-12 Cybersecurity Report — Annual threat analysis covering 5,000+ organizations
- U.S. Department of Education: Protecting Student Privacy — FERPA guidance and data security checklists
- NIST Cybersecurity Framework 2.0 — The risk management framework recommended for education
CISA's K-12 cybersecurity initiative, the CIS MS-ISAC program, and K12 SIX collectively form the primary defense infrastructure for U.S. educational institutions. All three offer services at no cost to qualifying schools and districts.
Sources: CIS MS-ISAC 2025 K-12 Cybersecurity Report, K-12 Dive: Ransomware in Education Jump 23%, K-12 Dive: 251 Ransomware Attacks in 2025, Infosecurity Magazine: CISO Spotlights Education, CISA K-12 Cybersecurity, DoE: Data Security for Education