The Three Numbers That Turn Cybersecurity Into a Budget Line Item
Every CISO has heard the question: "How much should we spend on security?" Annual Loss Expectancy (ALE) turns that vague anxiety into a dollar figure your CFO can actually work with. It is not a crystal ball. It is a framework for making informed bets instead of panicked ones.
ALE combines two inputs to produce one output:
| Component | What It Measures | Example |
|---|---|---|
| Single Loss Expectancy (SLE) | Cost of one incident | $50,000 per ransomware event |
| Annualized Rate of Occurrence (ARO) | How often it happens per year | 0.4 (once every 2.5 years) |
| Annual Loss Expectancy (ALE) | SLE x ARO | $50,000 x 0.4 = $20,000/year |
Step 1: Calculate Your Single Loss Expectancy (SLE)
SLE answers: "If this bad thing happens once, what does it cost us?" Include everything:
- Direct costs: Forensic investigation, legal fees, regulatory fines, ransom payments
- Operational costs: Downtime hours x hourly revenue, overtime for recovery teams
- Reputational costs: Customer churn, contract penalties, increased insurance premiums
- Recovery costs: Hardware replacement, data restoration, security hardening post-incident
For a 50-person company hit by ransomware, a realistic SLE might look like: $15,000 (forensics) + $10,000 (legal) + $20,000 (two days downtime) + $5,000 (recovery) = $50,000 SLE.
Step 2: Estimate Your Annualized Rate of Occurrence (ARO)
ARO answers: "How many times per year do we expect this to happen?" This is where the art meets the science. Sources to inform your estimate:
- Internal history: How many incidents of this type in the last 3-5 years?
- Industry data: The FBI IC3 2024 Annual Report provides sector-specific complaint volumes
- Vendor reports: Verizon DBIR, IBM Cost of a Data Breach, CrowdStrike Global Threat Report
- Professional judgment: Your security team's informed estimate, documented and reviewed annually
An ARO of 1.0 means once per year. An ARO of 0.1 means once per decade. Most SMB threat scenarios fall between 0.2 and 0.5.
Step 3: Multiply to Get ALE
ALE = SLE x ARO
That is the expected annual cost of a specific threat. If your ALE for ransomware is $20,000/year, then any countermeasure costing less than $20,000/year that meaningfully reduces either the SLE or ARO is a net positive investment.
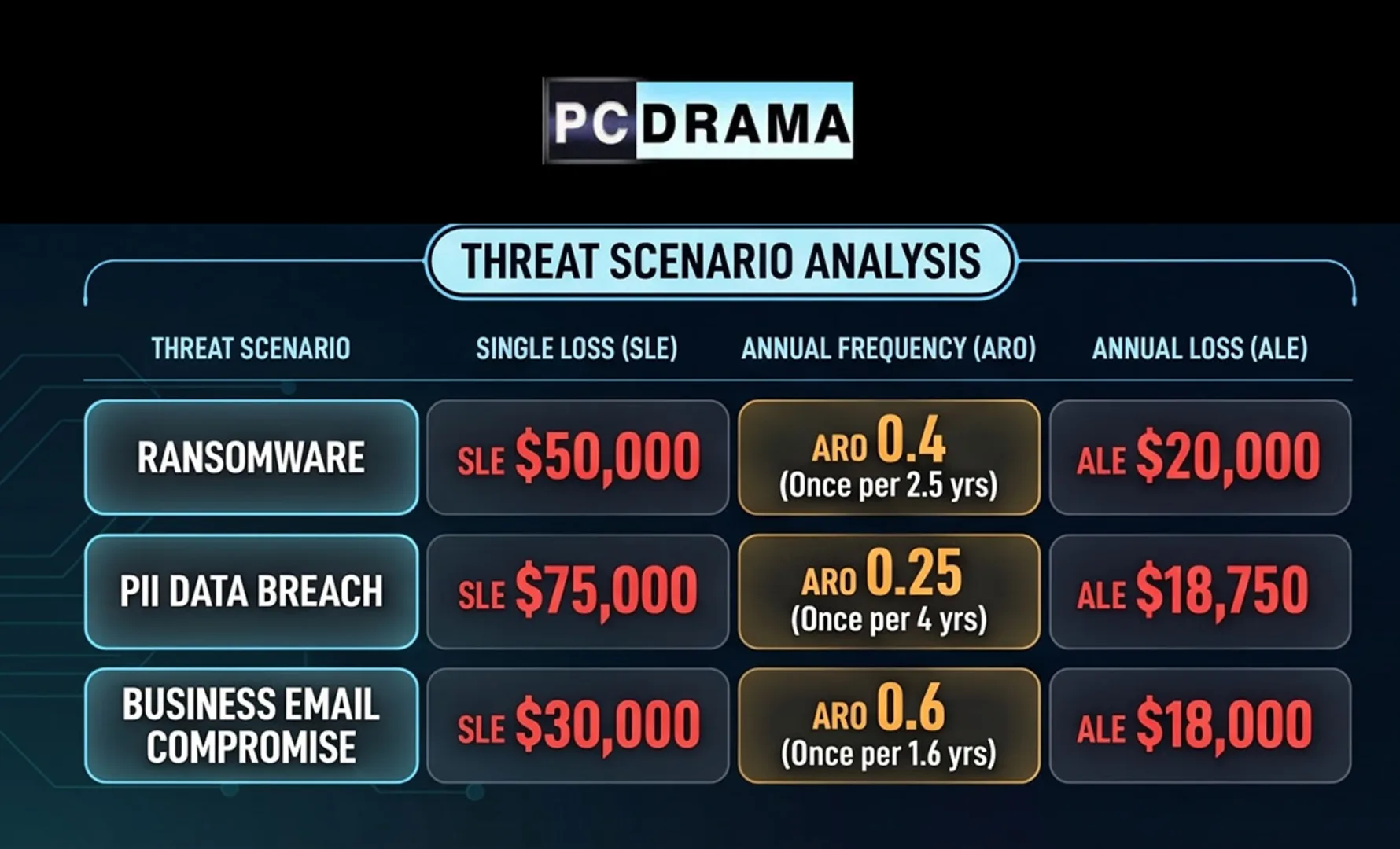
Practical Examples
| Threat Scenario | SLE | ARO | ALE |
|---|---|---|---|
| Ransomware (50-person firm) | $50,000 | 0.4 | $20,000 |
| PII breach on rental devices | $75,000 | 0.25 | $18,750 |
| Website defacement | $5,000 | 1.5 | $7,500 |
| Business email compromise | $30,000 | 0.6 | $18,000 |
| Insider data theft | $100,000 | 0.1 | $10,000 |
Using ALE to Justify Security Spending
The magic of ALE is in the comparison. If your ALE for a threat is $20,000 and a countermeasure costs $12,000/year while reducing the ARO by 80%, here is the math:
- New ALE: $50,000 x 0.08 = $4,000
- Risk reduction: $20,000 - $4,000 = $16,000 saved
- Net benefit: $16,000 saved - $12,000 cost = $4,000 net positive
That is how you turn "we need better endpoint protection" into "this investment returns $4,000 annually in reduced expected loss." CFOs understand that language.
Limitations Worth Knowing
ALE is a model, not a prophecy. Keep these caveats in mind:
- ARO estimates are subjective. Document your assumptions and review them annually against actual incident data.
- SLE can surprise you. Regulatory fines and reputational damage are notoriously hard to estimate upfront.
- ALE assumes independence. In reality, one breach can cascade into multiple loss categories simultaneously.
- It does not capture tail risk. A catastrophic once-in-a-century event will not show up in your ARO, but it could end your business.
Despite these limitations, ALE remains the most practical framework for moving cybersecurity conversations from "how much can we afford?" to "how much does it cost us not to?"
Sources: NIST Cybersecurity Framework, FBI IC3 2024 Annual Report, IBM Cost of a Data Breach Report 2024